Category: Site news
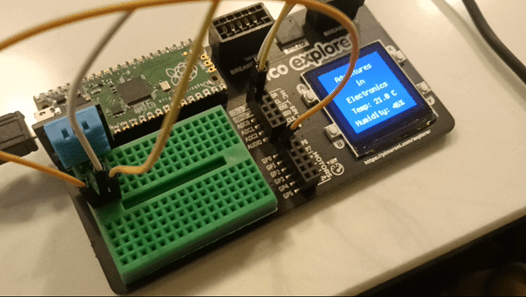
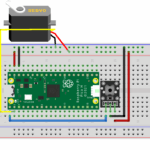
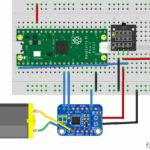
Adventures with Electronics
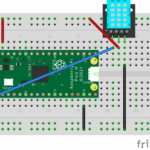
Adventures with Electronics is a father and son project to learn how to connect up and code 37...
Read MoreNew season of live.withcode.uk: free python resources for GCSE Computer Science
Well done to all the students (and teachers!) who worked so hard to prepare for the first ever...
Read MoreCompetitive code challenges in python
Series 2 of live.withcode.uk has launched with free weekly challenges to help students grow in...
Read MoreGCSE Computer Science resource updated to include OCR Exam Reference Language
To help students grow in confidence understanding and writing code (in pseudocode and a variety of...
Read MoreFree weekly python remote learning resources: update on new features
I’ve seen some really creative teaching and learning ideas to support students learning python programming during remote learning. Lots of teachers are looking for ways to stretch and support computing students while...
Read MoreFree weekly python remote learning activities
When the first lockdown started in March 2020 I wanted my Computing students to still be able to get some regular practice building up their skills and confidence with python programming, so I launched a series of weekly...
Read MoreFree primary computing remote learning resources
I am in awe of primary teachers who are managing to teach students in school and send out home...
Read MoreFree interactive python challenges for GCSE Computer Science
Keyword games for Topic 6 Programming Here’s a collection of free interactive python challenges for GCSE Computer Science. They’re designed to follow the Edexcel GCSE (first teaching 2020). This page is a work in...
Read MoreUsing create.withcode.uk to embed python code in an external website
Create.withcode.uk lets you write, run, debug and share python code in your browser. It’s designed for use in the classroom as a free online resource for teachers to help students grow in confidence, independence and...
Read Morelive.withcode.uk: Call for teachers to test new features
Well done to everyone who’s survived the first two weeks of remote learning: hats off to students who’ve got motivated to complete work at home; to teachers who’ve kept on top of remote learning whilst managing...
Read MoreComing soon: live.withcode.uk
I’ve been chatting to students, parents and other teachers about the best way to support them with remote learning during the Cornavirus school closures. I’m hoping to set up weekly live coding python video tutorials...
Read MoreComputing for all: Is GCSE Computer Science too hard for some students?
Summary: I don’t think GCSE CS is too hard for all students but the data here shows that steps need to be taken to make Computer Science more accessible to the students from the whole 9-1 ability range. Back in September...
Read More
Recent Posts
-
-
-
-
-
-
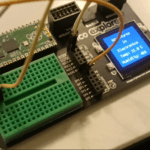 Adventures with ElectronicsDec 23, 2024 | Site news
Adventures with ElectronicsDec 23, 2024 | Site news -
-
 How do computers work? Part 2: CapacitorsMay 18, 2023 | How do computers work
How do computers work? Part 2: CapacitorsMay 18, 2023 | How do computers work -
 How do computers work? Part 1: IntroductionMay 18, 2023 | How do computers work
How do computers work? Part 1: IntroductionMay 18, 2023 | How do computers work -